BYOC PrivateLink¶
Some customers cannot allow any public network exposure on the dataplane that runs your application — typical for regulated industries, strict data-residency setups, and customers with zero-public-egress policies.
BYOC PrivateLink is a variant of BYOC where every byte of control-plane traffic between the customer's dataplane and your Omnistrate control plane flows over AWS PrivateLink. The dataplane EKS cluster has no public endpoint and no internet-facing load balancers for control traffic.
Note
BYOC PrivateLink is currently supported on AWS. The customer's VPC and your provisioner VPC may live in different AWS regions.
How to Enable BYOC PrivateLink¶
BYOC PrivateLink is selected per customer account, at account onboarding time. Once an account is onboarded with PrivateLink enabled, every instance deployed into that account uses the PrivateLink dataplane topology — there is no per-instance toggle and no compose-spec change required.
Customer Portal¶
When your customer onboards their AWS account into a BYOC Plan from the customer portal, they enable the PrivateLink connectivity option on the AWS account form. The portal then issues the bootstrap CloudFormation link and tracks the account as PrivateLink-enabled.
omnistrate-ctl¶
omnistrate-ctl account customer create \
--service=<service> \
--environment=<environment> \
--plan=<plan> \
--customer-email=<customer@example.com> \
--aws-account-id=<AWS_ACCOUNT_ID> \
--private-link
The --private-link flag enables AWS PrivateLink connectivity for every instance deployed into this account. See the account customer create reference for all flags.
BYOC PrivateLink Architecture¶
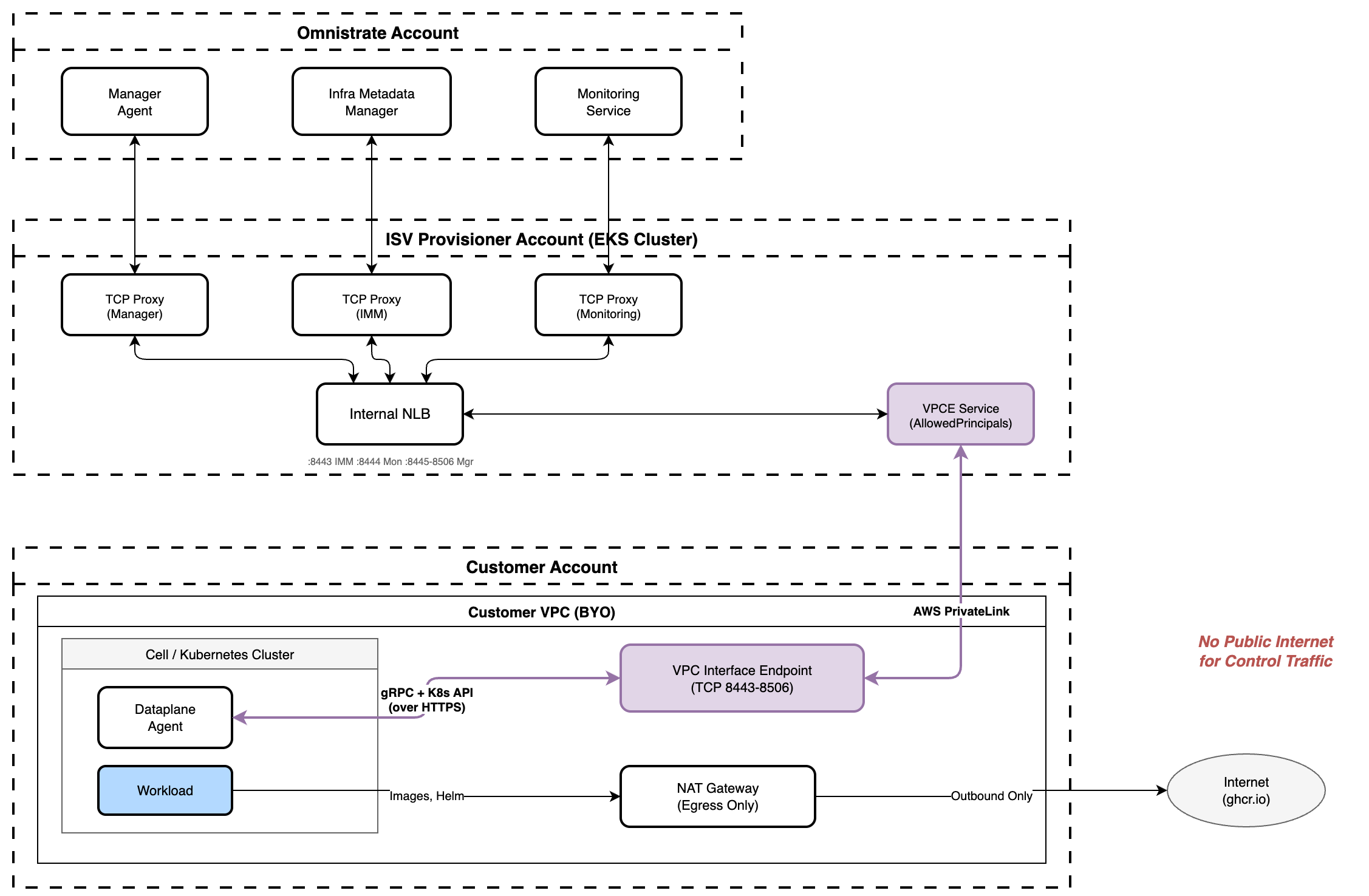
There are two communication paths, both private:
- Dataplane → Control plane (PrivateLink). The dataplane agent reaches Omnistrate services (manager agent, infra metadata manager, monitoring) through a customer-owned VPC Interface Endpoint that targets your provisioner's PrivateLink service (NLB + TCP Proxy).
- Control plane → Dataplane (PrivateLink). The manager agent reaches back to the dataplane agent through the same PrivateLink path — TCP Proxy → NLB → VPCE Service → customer VPC Endpoint → dataplane agent.
Both gRPC and K8s API traffic flow over HTTPS through this bidirectional PrivateLink connection. No public internet is used for control traffic.
When a PrivateLink account onboards for the first time, Omnistrate automatically configures the provisioner side: TCP proxies, internal NLB, the VPCE service, and the customer's account on the service's AllowedPrincipals list.
Customer VPC Topology¶
Your customer can pick one of two VPC topologies for the dataplane:
- Omnistrate-managed VPC — Omnistrate provisions the VPC, subnets, NAT gateway, security group, and the management VPCE on first deployment. Requires the Allow new cloud-native network creation option (or
--allow-create-new-cloud-native-network) when the account is onboarded. See Omnistrate-managed VPC. - Customer-owned (imported) VPC — Customer provides an existing VPC + subnets and creates the management VPCE themselves. See Imported VPC requirements for BYOC PrivateLink for the exact tags, security-group ports, and cross-region constraints.